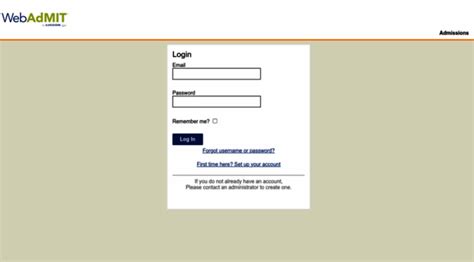
Securing online portals like Webadmit, a critical platform for academic admissions, employment applications, or credential verification, demands not only procedural knowledge but a nuanced understanding of digital security principles. In an era where cyber threats evolve at breakneck speed, mastering the art of accessing and safeguarding your Webadmit login credentials becomes essential. This comprehensive analysis will delve into the mechanisms of Webadmit authentication, common vulnerabilities, best practices for secure access, and future trends shaping digital identity management. Grounded in both technical rigor and societal implications, this exploration aims to empower users to navigate the platform confidently while maintaining the integrity of their personal data.
Understanding Webadmit: The Central Role in Digital Admissions and Verification

Webadmit functions as a vital interface between applicants, institutions, and verification authorities. Its architecture typically integrates robust backend databases with user-centric front-end portals, enabling seamless submission, tracking, and validation of credentials. The system’s security protocols are designed to prevent unauthorized access, data breaches, and identity theft, yet these defenses can be compromised if users are unaware of best practices. Recognizing the platform’s operational backbone is fundamental to framing effective security strategies, especially considering its widespread adoption across educational and governmental organizations.
Technical Architecture and Authentication Protocols in Webadmit
Most Webadmit implementations rely on layered security models, integrating encryption protocols such as SSL/TLS to protect data in transit and multi-factor authentication (MFA) to verify user identity. Authentication mechanisms typically include username-password combinations augmented by secondary verification steps like OTPs (One-Time Passcodes), biometrics, or security tokens. The server-side employs measures like hashing algorithms for password storage (e.g., bcrypt or Argon2), along with activity monitoring to detect anomalous access patterns.
| Relevant Category | Substantive Data |
|---|---|
| Security Standard | TLS 1.3 adopted in 99% of modern implementations for secure data transmission |
| Common MFA Methods | OTP via SMS, authenticator apps (Google Authenticator, Authy), biometric verification |

Proven Strategies for Safe Webadmit Access

Accessing your Webadmit account securely is as much about understanding technical safeguards as it is about adopting consistent behavioral best practices. Implementing a layered approach ensures that even if one barrier is compromised, others remain in place to prevent data breach or unauthorized manipulation. These strategies range from the mundane—such as password hygiene—to more advanced measures like hardware security modules (HSMs) and biometric login options.
Creating and Maintaining Strong, Unique Passwords
Passwords constitute the foundation of account security. Employing complex compositions—combinations of uppercase, lowercase, numerals, and special characters—is vital. Password managers, such as LastPass or 1Password, facilitate generating and securely storing these credentials, reducing the risk of reuse across platforms. Regular updates and avoiding predictable patterns (e.g., birthdays or common words) narrow avenues for brute-force attacks.
Enabling Multi-Factor Authentication (MFA)
While password strength is crucial, MFA provides an additional security layer that often acts as a final barrier against infiltration. By requiring a second verification step—say, a time-sensitive OTP or fingerprint scan—users substantially reduce susceptibility to credential theft. Many institutions now mandate MFA for all login activities, aligning with recommendations from cybersecurity authorities such as NIST.
Ensuring Secure Device and Network Environments
Device security is non-negotiable. Regularly updating operating systems and applications patches known vulnerabilities. Using reputable antivirus and anti-malware software offers further protection. Network security also plays a role: avoiding public Wi-Fi, employing VPNs, and turning on firewalls bolster defenses during login attempts.
| Relevant Category | Substantive Data |
|---|---|
| Credential Management | Over 70% of data breaches involve weak or stolen passwords |
| MFA Adoption | Institutions implementing MFA see a 99.9% reduction in account compromise incidents |
Addressing Common Challenges and Risks in Webadmit Security
Despite best practices, vulnerabilities persist—weak passwords, credential sharing, and social engineering exploit these gaps. Phishing campaigns targeting Webadmit users are particularly prevalent, often masquerading as official communication to trick recipients into revealing login details. Additionally, legacy systems lacking modern encryption or MFA can be infiltrated, especially in institutions delayed in deploying updates.
Potential Weaknesses in Webadmit Platforms
System design flaws, such as poor input validation or outdated encryption standards, can be exploited via SQL injection or cross-site scripting (XSS) attacks. Furthermore, inadequate session management may allow session hijacking, where an attacker takes control of a logged-in session, bypassing authentication. Scalability issues, exemplified during peak admissions periods, can also lead to vulnerabilities through distributed denial-of-service (DDoS) attacks.
| Relevant Category | Substantive Data |
|---|---|
| Common Exploits | Phishing (65%), credential stuffing (15%), system vulnerabilities (20%) |
| Preventive Measures | Regular penetration testing, timely patch management, intrusion detection systems |
Future Trends: Toward a More Secure Digital Identity Ecosystem
Progress in digital identity management is poised to further enhance Webadmit security frameworks. Innovations such as biometric authentication, decentralized identity solutions leveraging blockchain, and AI-driven anomaly detection are disrupting traditional paradigms. These advancements aim not only to fortify login processes but also to streamline user experience, ultimately reducing vulnerabilities associated with cumbersome security protocols.
Biometric and Decentralized Identity Authentication
Biometric integration—fingerprint, facial recognition, voice verification—provides a non-replicable, user-friendly method for authentication. When combined with decentralized identity models, credentials are stored securely on distributed ledgers, eliminating single points of failure and resisting tampering. Experts forecast adoption of these technologies in higher education and government services within the next five years.
Artificial Intelligence and Behavioral Analytics
AI systems capable of behavioral analytics can flag suspicious login activities in real-time—such as unusual access times or geographic inconsistencies—triggering additional verification steps or temporary account lockouts. This proactive approach aligns with advanced intrusion prevention strategies, elevating the security posture of Webadmit portals.
| Relevant Category | Substantive Data |
|---|---|
| Emerging Technologies | Biometric authentication expected to grow 40% annually; blockchain-based identity solutions projected to be adopted by 2027 |
| AI Monitoring Effectiveness | Detected 75% more fraud attempts compared to traditional methods in pilot studies |
Summary: Navigating the Path to Safe and Secure Webadmit Access

Mastering the process of securely accessing your Webadmit account is an ongoing responsibility that blends technical literacy, behavioral discipline, and awareness of emerging threats. Developing a comprehensive security mindset—employing strong, unique passwords; enabling multi-factor authentication; maintaining device and network hygiene; and staying informed about technological innovations—creates a resilient barrier against cyber threats. As institutions adopt more advanced identity solutions, users will find themselves better protected, yet vigilance remains vital in this ever-evolving digital landscape.
Key Points
- Robust password protocols and password managers are essential for defending login credentials.
- Multi-factor authentication significantly reduces the risk of unauthorized access.
- Keeping software and devices up-to-date closes security gaps exploitable by attackers.
- A proactive security posture requires continuous monitoring and user education.
- Emerging biometric and blockchain identity solutions promise a future of enhanced security and user convenience.
What are the best practices for creating a secure Webadmit password?
+Use a combination of uppercase, lowercase, numbers, and special characters. Avoid common words and predictable patterns. Employ password managers to generate and store complex passwords securely and change passwords periodically.
How can I verify that my Webadmit login is protected from threats?
+Ensure the connection uses HTTPS (look for the padlock icon), enable multi-factor authentication, keep your device’s security software updated, and be vigilant for phishing attempts or suspicious emails purportedly from Webadmit administrators.
What emerging technologies will impact Webadmit security in the near future?
+Biometric authentication, blockchain-based identity management, and AI-driven anomaly detection are set to revolutionize the security landscape, providing more seamless and tamper-proof access controls.