A comprehensive system security plan is a crucial component of any organization's overall cybersecurity strategy. It serves as a roadmap for protecting against various types of threats, ensuring the confidentiality, integrity, and availability of sensitive data and systems. Developing and implementing such a plan requires a deep understanding of the organization's security posture, including its assets, vulnerabilities, and potential risks. In this article, we will delve into the key elements of a system security plan, discussing its importance, the process of creating one, and the essential components that must be included to ensure its effectiveness.
Key Points
- Conducting a thorough risk assessment to identify potential vulnerabilities and threats
- Implementing a layered security approach to protect against various types of attacks
- Developing incident response and disaster recovery plans to ensure business continuity
- Providing regular security awareness training to employees and stakeholders
- Continuously monitoring and updating the system security plan to address emerging threats and technologies
Understanding the Importance of a System Security Plan

A system security plan is essential for safeguarding an organization’s critical assets and data from cyber threats. The plan outlines the policies, procedures, and controls necessary to manage and mitigate risks, ensuring the security and integrity of the organization’s systems and data. It also helps to comply with regulatory requirements and industry standards, reducing the risk of non-compliance and associated penalties.
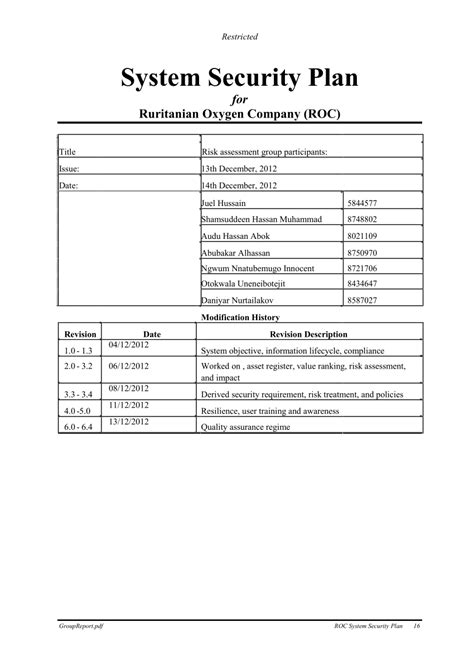
Risk Assessment and Vulnerability Management
Risk assessment is a critical component of a system security plan, involving the identification, analysis, and prioritization of potential risks to the organization’s systems and data. This process helps to identify vulnerabilities and threats, allowing for the implementation of controls and mitigation strategies to reduce the risk of a security breach. Vulnerability management is an ongoing process that involves regularly scanning for and remediating vulnerabilities, ensuring that the organization’s systems and software are up-to-date and secure.
| Category | Description |
|---|---|
| Risk Assessment | Identification, analysis, and prioritization of potential risks |
| Vulnerability Management | Regular scanning and remediation of vulnerabilities |
| Incident Response | Planning and procedures for responding to security incidents |
| Disaster Recovery | Planning and procedures for recovering from disasters and major security incidents |
Implementing a Layered Security Approach
A layered security approach involves implementing multiple security controls and measures to protect against various types of attacks. This may include firewalls, intrusion detection and prevention systems, encryption, access controls, and security awareness training. Each layer provides an additional level of protection, making it more difficult for attackers to breach the organization’s systems and data.
Incident Response and Disaster Recovery Planning
Incident response and disaster recovery planning are critical components of a system security plan, outlining the procedures and protocols for responding to and recovering from security incidents and disasters. These plans help to minimize downtime, reduce the impact of a security breach, and ensure business continuity. They should be regularly tested and updated to ensure their effectiveness and relevance.
Security Awareness Training and Education
Security awareness training and education are essential for ensuring that employees and stakeholders understand the importance of cybersecurity and their role in protecting the organization’s systems and data. Regular training sessions should be provided to educate individuals on security best practices, phishing attacks, and other types of cyber threats. This helps to reduce the risk of human error and insider threats, which are often the most significant vulnerabilities in an organization’s security posture.
Continuous Monitoring and Update
A system security plan should be continuously monitored and updated to address emerging threats and technologies. This involves regularly reviewing and assessing the plan’s effectiveness, identifying areas for improvement, and implementing changes as needed. Continuous monitoring and update help to ensure that the organization’s security posture remains robust and effective, protecting against the latest cyber threats and vulnerabilities.
What is the primary purpose of a system security plan?
+The primary purpose of a system security plan is to protect an organization's critical assets and data from cyber threats, ensuring the confidentiality, integrity, and availability of sensitive information.
How often should a system security plan be reviewed and updated?
+A system security plan should be regularly reviewed and updated to address emerging threats and technologies, ideally every 6-12 months or as needed.
What is the importance of security awareness training in a system security plan?
+Security awareness training is essential for ensuring that employees and stakeholders understand the importance of cybersecurity and their role in protecting the organization's systems and data, reducing the risk of human error and insider threats.
In conclusion, a comprehensive system security plan is a critical component of an organization’s overall cybersecurity strategy, providing a roadmap for protecting against various types of threats and ensuring the confidentiality, integrity, and availability of sensitive data and systems. By implementing a layered security approach, conducting regular risk assessments, and providing security awareness training, organizations can reduce the risk of cyber threats and protect their critical assets. Continuous monitoring and update of the plan are essential to ensure its effectiveness and relevance in the face of evolving cyber threats and technologies.